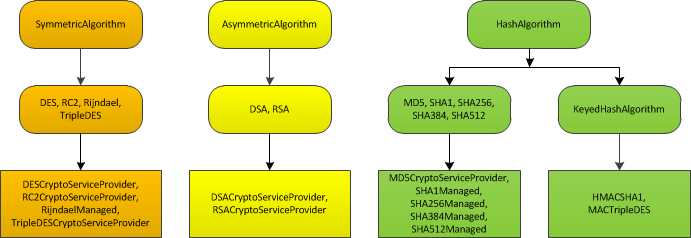
The .NET encryption classes are divided into three layers.
1. The first layer is a set of abstract base classes and these classes represent an encryption task. The next table lists these classes:
|
Class name |
Description |
| SymmetricAlgorithm |
This class represents symmetric encryption, which uses a shared secret value. Data encrypted with the key can be decrypted using only the same key. |
| AsymmetricAlgorithm |
This class represents asymmetric encryption, which uses a public/private key pair. Data encrypted with one key can be decrypted only with the other key. |
| HashAlgorithm |
This class represents hash generation and verification. Hashes are also known as one-way encryption algorithms, because you can only encrypt but not decrypt data. You can use hashes to ensure that data is not tampered with. |
2. The second level includes classes that represent a specific encryption algorithm. They derive from the encryption base classes, but they are also abstract classes. For example, the DSA algorithm class, which represents the DSA (Digital Signature Algorithm), derives from AsymmetricAlgorithm.
3. The third level of classes is a set of encryption implementations. Each implementation class derives from an algorithm class. This means a specific encryption algorithm such as DSA could have multiple implementation classes. Although some .NET Framework encryption classes are implemented entirely in managed code, most are actually thin wrappers over the CryptoAPI library. The classes that wrap the CryptoAPI functions have CryptoServiceProvider in their name (for example, DSACryptoServiceProvider), while the managed classes typically have Managed in their name (for example, SHA1Managed).
Note: The managed classes perform all their work in the .NET world under the supervision of the CLR, while the unmanaged classes use calls to the unmanaged CryptoAPI library.
The next picture shows the classes in the System.Security.Cryptography namespace:
Important notes:
1. You can create a new implementation for an existing cryptography class by deriving from an existing algorithm class. For example, you could create a class that implements the RSA algorithm entirely in managed code by creating a new RSAManaged class and inheriting from RSACryptoServiceProvider.
2. You can add support for a new encryption algorithm by adding an abstract algorithm class (for example, the CLONE256 algorithm, which is similar to the RC2 algorithm but is not provided in the framework) and a concrete implementation class (such as, for example, CLONE256Managed if you want to implement the CLONE256 algorithm).